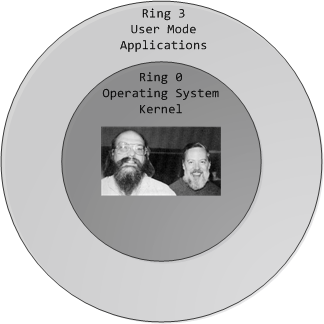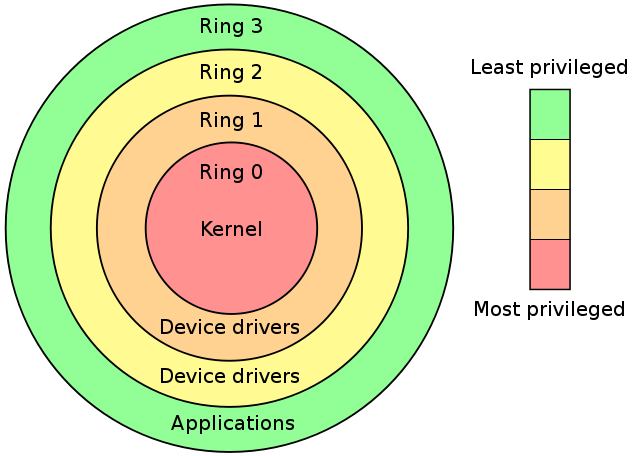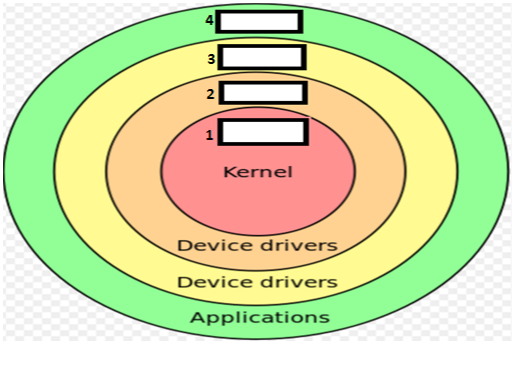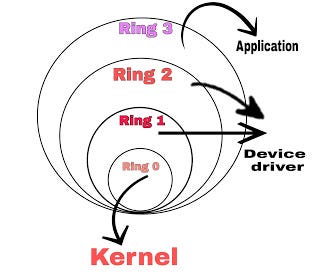
What is kernel rings in a system ? | kernel protection ring | cloudpradeep | by cloud pradeep | Medium
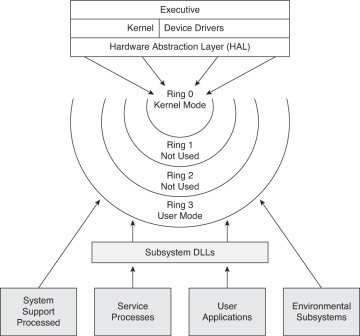
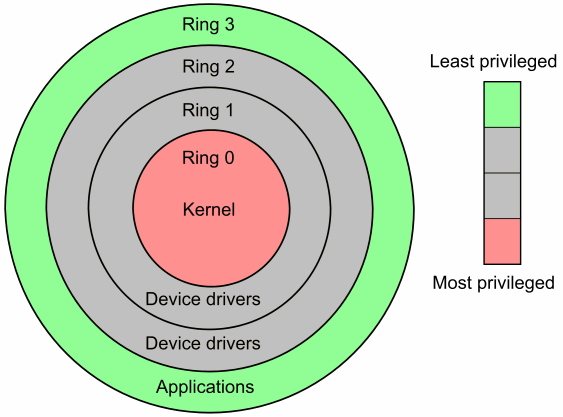
Security Architecture | CISSP Exam Cram: Security Architecture and Models | Pearson IT Certification
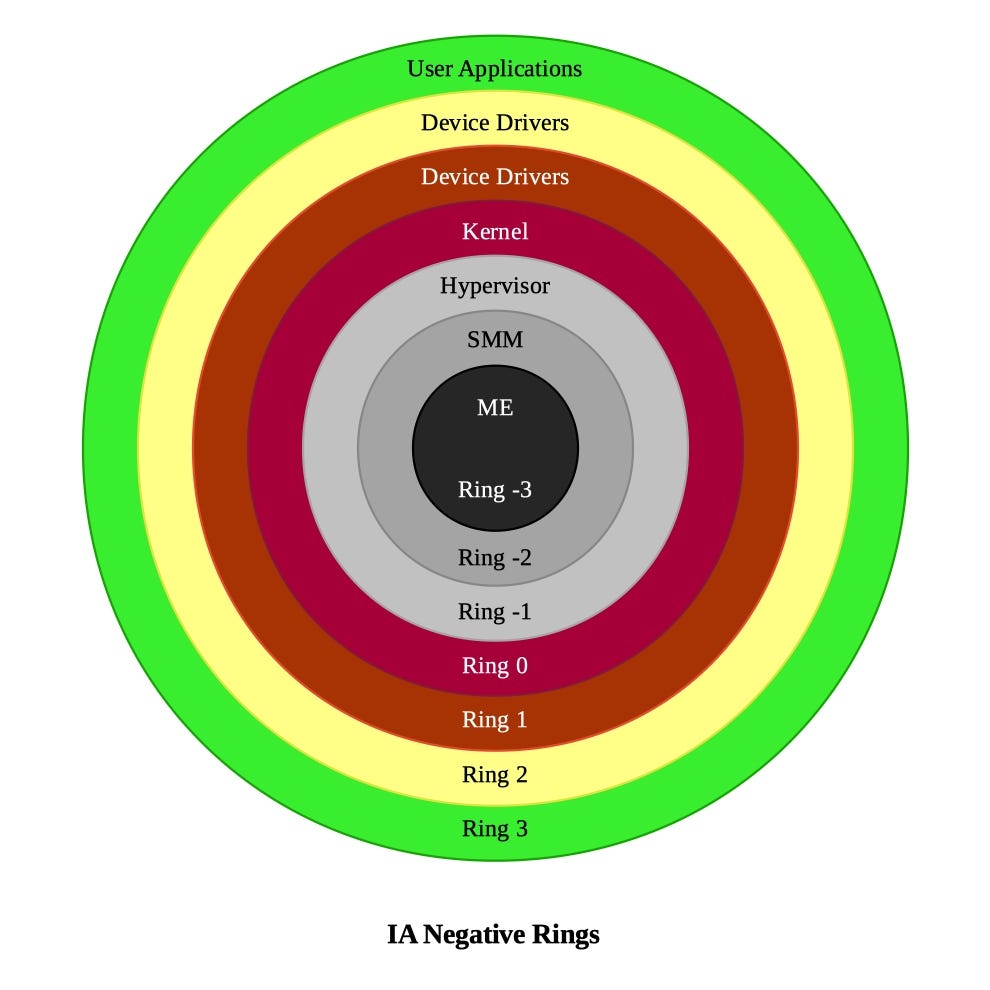
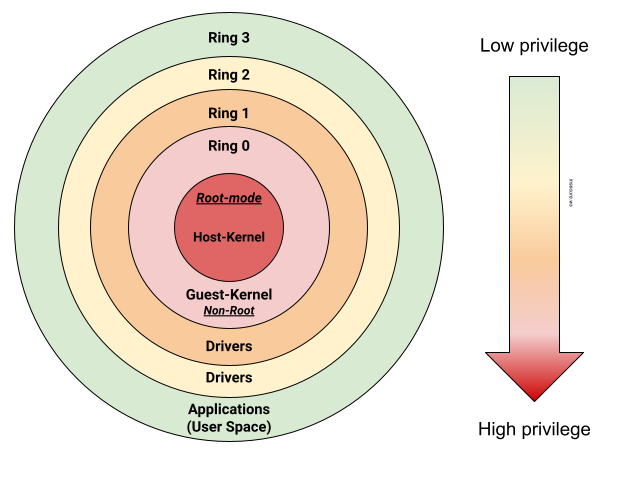
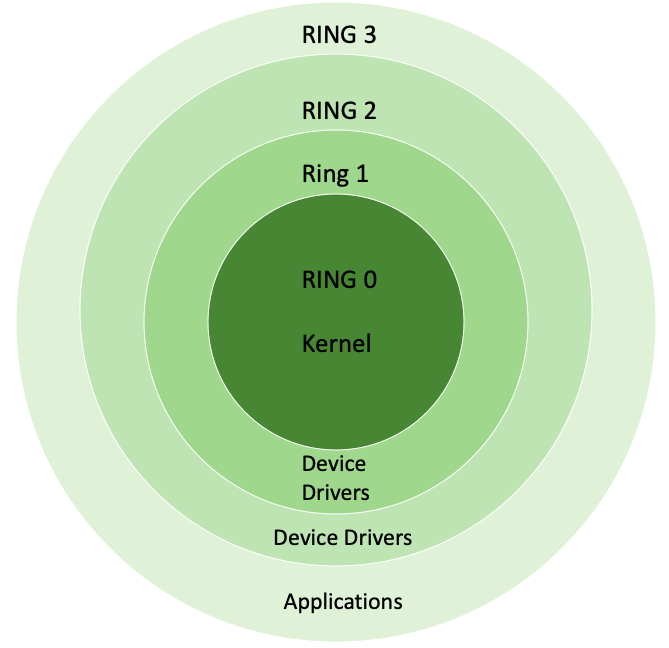
Negative Rings in Intel Architecture: The Security Threats That You've Probably Never Heard Of | by RealWorldCyberSecurity | The Startup | Medium


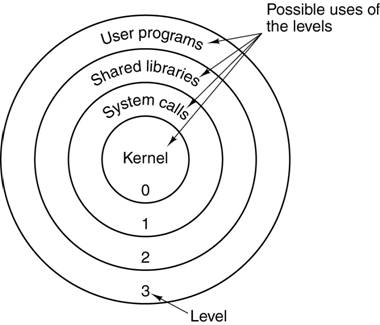
![Intel's Ring Architecture [28, 37, 24, 14] | Download Scientific Diagram Intel's Ring Architecture [28, 37, 24, 14] | Download Scientific Diagram](https://www.researchgate.net/publication/50875025/figure/fig2/AS:671525288038404@1537115513180/Intels-Ring-Architecture-28-37-24-14.png)